According to a Forbes Tech Council study, the distributed nature of contemporary workforces presents significant challenges, as demonstrated by the fact that 72% of Chief Information Security Officers (CISOs) agree that remote work has complicated their organization’s cybersecurity environment. The risk of being exposed to cyber threats significantly rises as employees access company data from a variety of devices and locations, frequently outside of conventional secure perimeters. Legacy security models, which mainly depended on protecting a fixed network boundary, are put under pressure by this expanded attack surface.
Cybersecurity expert and author Bruce Schneier once said, “You cannot defend. You cannot prevent. The only thing you can do is detect and respond.”As the Zero Trust approach emphasizes ongoing monitoring and flexible responses to protect remote work environments, it highlights the importance of continuous surveillance and real-time verification in contemporary security strategies.
Although the flexibility of remote work increases productivity and employee satisfaction, it also creates risks, including the use of unmanaged personal devices, unsecured home networks, and an increased susceptibility to social engineering and phishing attacks. Therefore, companies need to implement security frameworks that require constant verification and stringent access controls rather than relying on implicit trust based on location or network.
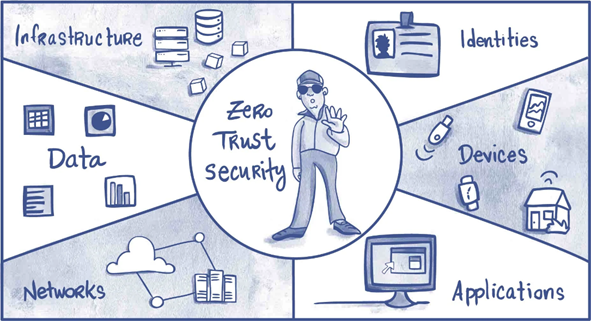
As a suitable solution, zero trust security—an adaptive model that demands strict identity verification and least-privilege access at every stage—emerges. In an era where work can be done anywhere, at any time, this innovative approach safeguards sensitive resources by bridging the gap between flexibility and security.
Strengthening Identity Verification and Access Control
Ensuring that only verified users have access to sensitive company resources is crucial in remote work environments. Zero trust, in contrast to conventional security models, employs methods such as centralized identity and access management (IAM) and multi-factor authentication (MFA) to enforce ongoing identity verification. This strategy successfully reduces the risks of unauthorized access and credential theft, particularly when staff members connect from unprotected or personal devices.
Further reducing the possibility of security breaches is the implementation of the principle of least privilege, which guarantees that users have access to only the resources necessary for their roles. To enhance threat detection and response capabilities, organizations are incorporating AI and automation into their security systems and refining their methodologies. This trend further supports the importance of sophisticated identity verification in contemporary cybersecurity. Auxin Security empowers organizations by providing a balanced approach to access management and identity verification, when combined with innovative security services, to help companies maintain strong defenses in remote environments.
Using Network Micro-Segmentation to limit threats
By breaking up corporate networks into more manageable, isolated sections, a technique known as micro-segmentation, zero trust goes beyond perimeter security. Because of this change in architecture, an attacker’s ability to move laterally across the network is significantly limited, even if they manage to compromise one area. When a workforce is dispersed and devices connect from locations outside of conventional office boundaries, containment is critical.
Organizations can reduce exposure and better contain threats by carefully segmenting the network according to user roles, application sensitivity, or device type. Zero Trust Architecture is a security framework that enhances security against evolving threats by continuously verifying the legitimacy of users, devices, and applications. This illustrates how crucial micro-segmentation is as a fundamental tenet in dynamically reducing the extent of breaches. The cloud and container security expertise of Auxin Security ensures accurate micro-segmentation strategies that enhance an organization’s overall security posture without compromising operational agility.
Continuous Monitoring and Threat Detection
More than just initial authentication is needed to maintain security in remote work settings; ongoing, real-time monitoring of user behavior, device health, and access patterns is also necessary. Zero-trust frameworks utilize advanced logging and analytics to rapidly identify anomalies that may indicate a breach, such as unusual login locations or suspicious device configurations.
When users connect over erratic home or public networks, this proactive vigilance is essential. Quick incident response is made possible by rapid threat detection, which reduces potential damage. By utilizing cutting-edge AI-driven threat detection and proactive security measures, Auxin Security enhances this capability, enabling organizations to stay ahead of evolving cyber threats through ongoing, intelligent monitoring.
Using Smart Tech for Better Security
Organizations must utilize complementary technologies that strengthen each security layer to adopt zero trust fully. By adding a crucial verification step, multi-factor authentication (MFA) significantly lowers the risk of unwanted access. Identity and Access Management (IAM) systems streamline governance in distributed environments by offering centralized visibility and control over user permissions.
Tools for device security and endpoint compliance ensure that only reliable devices have access to company data, which is crucial in BYOD situations frequently encountered in remote work environments. In the meantime, malware and phishing attempts are actively blocked by sophisticated threat protection tools, such as sandboxing and AI-powered analysis. By integrating these technologies into modified strategies, Auxin Security’s comprehensive cloud cybersecurity and DevSecOps consulting helps businesses create a scalable and resilient zero-trust infrastructure that fulfills their operational requirements.
Staying Secure in a Remote World
More than 70% of security leaders acknowledge the increasing complexity of protecting distributed workforces by 2025, as remote work continues to grow rapidly. Zero Trust provides an effective structure necessary for today’s adaptable work environments by continuously verifying identities, segmenting networks, and staying up-to-date on threats in real-time. Auxin Security helps businesses adopt this flexible strategy by combining innovative equipment with expert services to safeguard vital assets wherever work is conducted.